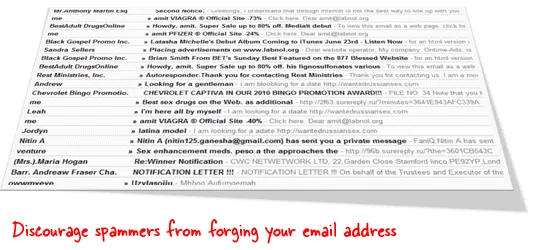
The majority of email spam on the Internet originates from forged addresses because SMTP allows any computer to send emails claiming to be from anyone.
For instance, a spammer can put your email address in the “From” field when sending out bulk emails and the recipients may therefore incorrectly assume that the mail is coming from you. If any of them chooses to report that spoofed message as spam, its your email address that will be affected in the long run.
Authenticate your Google Workspace Domain with SPF
To prevent spammers from forging the “From” field of their bulk messages with your email address, you can consider using a validation system like SPF (short for Sender Policy Framework). It basically allows the email recipients to verify that the server sending the email is authorized to send email on behalf of the domain that is found in the sender’s email address.
Let me explain. If the IP address of my mail server is 1.2.3.4, I can add an SPF record to my web domain saying that all messages coming from this particular IP address. ISPs can match the mail server address mentioned in my domain’s SPF record against the one present in my emails and accordingly pass or bounce messages to their customers.
How to Implement SPF in Google Workspace
Let’s say you have a Google Workspace domain at xyz.com and you are using the Gmail service for your incoming and outgoing email.
To add an SPF record to your domain, first open the page from where you can edit your domain’s DNS records. Then add a new DNS record of type “TXT” and set the value as
v=spf1 include:_spf.google.com ~allSave the changes and this new DNS record should propagate across the Internet within the next few hours. If you are interested in the technical details, here they are are:
The entry _spf.google.com means that any server that is allowed to send mail from the IP addresses of Google Workspace mail servers is also allowed to send mail from labnol.org. The ~all directive means that email messages that are not sent from an approved server should still be accepted but may be subjected to greater scrutiny.
How to Check SPF Records of your Google Workspace Domain
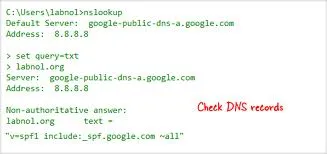 To ensure that your SPF record has been successfully added to your web domain, open your command prompt - go to Windows Start Menu -> Run and type cmd.
To ensure that your SPF record has been successfully added to your web domain, open your command prompt - go to Windows Start Menu -> Run and type cmd.
Nex run the nslookup command for your Google Workspace Domain as shown below:
nslookup
set query=txt
xyz.com (replace xyz.com with your Google Workspace domain name)If the answer contains the google.com string that you have added in the previous step, it indicates that SPF is successfully enabled for your Google Workspace.
Verify SPF Records with an Email Message
Finally, to verify that your SPF record is live and working, just send a blank email message to check-auth@verifier.port25.com from your Gmail address.
You’ll get an instant reply with the results of the SPF check. If you see a “pass” against the SPF check, that means things are in place and it should prevent your Gmail messages from getting rejected as spam because now the recipient can distinguish forged emails from the real ones with a simple check.


